Cyber threats have grown in frequency and sophistication in recent years, so it is only natural that institutions are expanding their protections. In addition to cybersecurity solutions and increased personnel training, cyber liability insurance serves as another layer of protection for institutions in the event of an attack. Cyber liability insurance helps institutions cope with the financial ramifications of a cyber incident.
What is cyber liability insurance?
Cyber liability insurance, also known as cyber insurance, is a type of insurance policy designed to provide businesses with coverage in the aftermath of a cyberattack, minimizing disruption and covering some costs of the incident. According to the FFIEC, “use of cyber insurance may offset financial losses resulting from cyber incidents.” Such incidents can include data breaches that result in the loss of sensitive customer information as well as other types of cyberattacks.
The demand for cyber insurance among businesses is accelerating, as 50% of companies have some type of cyber insurance compared to 34% two years ago. As a reminder, cyber insurance is not a substitution for a holistic cybersecurity strategy and should be used in conjunction with other security layers since it will not prevent a cyberattack.
What does cyber liability insurance cover?
The interest in cyber insurance is in part spurred by the fact that traditional insurance policies for general liability or basic business interruption coverage may not fully cover cyber risk exposures. Coverage may also be limited and not cover incidents caused by or tracked to outside vendors.
Like most insurance, there are different types of cyber insurance to consider. According to the Federal Trade Commission, first-party coverage protects your data—including employee and customer information—and includes costs related to legal counsel, recovery of lost or stolen data, crisis management, forensic services to investigate the breach and more. Meanwhile, third-party coverage protects your institution from liability if a third party files claims against you, and includes payments to consumers affected, costs for litigation or settlements.
Who needs cyber liability insurance?
In short, any business that stores or manages data online, including personally identifiable information or bank account information, could benefit from cyber insurance. This holds especially true for financial institutions.
In CSI’s 2022 Banking Priorities Executive Report, bankers reported ransomware as one of the top cyber threats this year. While the costs of a cyberattack vary based on the severity of the attack, financial institutions hold valuable data, incentivizing cybercriminals to levy sizeable ransoms. Additionally, any downtime resulting from a cyberattack would be costly to a financial institution, and cyber insurance mitigates that risk since it would aid in recovery from an attack.
 Any business that stores or manages data online–including financial institutions– could benefit from cyber liability insurance.
Any business that stores or manages data online–including financial institutions– could benefit from cyber liability insurance.
Should financial institutions require cyber insurance for their business customers?
There is a hidden risk for financial institutions engaging in commercial lending as it relates to cyberattacks. It is common for a ransomware attack to freeze operations for the duration of the incident or until the ransom is paid—which could last days, weeks or months—and many businesses cannot support such a disruption. While these businesses could have business interruption insurance that covers lost profitability, it is not enough to keep most organizations afloat long term if their operations or reputation are significantly affected by an attack. This presents a massive risk not only to small- and mid-sized businesses (SMBs), but also to the institution through which they secured a commercial loan.
Consider this alarming statistic: According to research from the National Cyber Security Alliance, 60% of SMBs fail six months after suffering from a cyberattack. Additionally, the 2022 Verizon Data Breach Report found a 13% increase in ransomware this year—more than the last five years combined—and 61% of all SMBs reported at least one cyberattack during the previous year.
If one or more of your commercial loan customers gets hit with a ransomware attack and goes out of business before the term of their loan ends, that directly affects your loan portfolio. And many SMBs do not have cyber insurance or even a formal plan for dealing with the aftermath of an attack. Requiring cyber insurance and minimal cybersecurity controls for commercial borrowers is one strategy to mitigate this risk.
 60% of small and mid-sized businesses fail six months after experiencing a cyberattack, making cyber insurance critical.
60% of small and mid-sized businesses fail six months after experiencing a cyberattack, making cyber insurance critical.
How much does cyber insurance cost?
The surge in ransomware attacks is causing cyber insurance premiums to rise, as carriers dole out hefty payouts. Pricing for cyber insurance varies by provider and policy, and carriers require organizations to have security controls in place to mitigate their risk. When selecting a provider and policy, thoroughly review the policy to ensure you meet the requirements and the amount of coverage delivers the protection your institution needs. Despite the rising costs of cyber insurance, it will cost an institution more in the long run to experience an attack without coverage in most incidents.
Best Practices for Meeting Cyber Liability Insurance Requirements
As demand spikes for cyber insurance, carriers are stepping up their game to require specific security controls and expanding the scope of areas they are concerned with. Carriers can deny coverage if institutions do not have proper security measures in place or misrepresent their security controls.
Institutions now looking at cyber insurance will have to prove they are actively working to minimize risk. As the threat landscape evolves, it’s likely that carriers will start wanting to see institutions’ audit results or begin requiring them to work with auditing firms to undergo a cyber insurance-specific audit.
In the meantime, consider implementing the following security controls commonly referenced on cyber insurance applications to strengthen your cybersecurity posture.
Harden Credentials with Multi-Factor Authentication
From a regulatory perspective, multi-factor authentication (MFA) is no longer an optional control. With MFA, a user needs an additional piece of information along with their username and password to verify their identity and log into an account. Because of the additional protection MFA offers against unauthorized account takeovers, the regulatory language surrounding MFA has shifted from “could” or “may” to “must” or “should.”
Cyber insurance carriers increasingly perceive the lack of MFA for privileged accounts—or accounts with administrative privileges—as an unacceptable risk and will not underwrite a cyber policy if these accounts are not hardened. From a risk perspective, the increase in malicious cyber activity, especially around privileged account access, will continue to escalate. MFA is an effective control to mitigate many aspects of the inherent risk.
At this stage, MFA applied to all network/domain accounts for accessing a laptop or PC is not a regulatory or carrier requirement. The cost and friction created by using the MFA control layer in this manner across an entire enterprise are hard to justify. From a security and business perspective, it makes more sense to allocate those budgetary resources to other controls with greater potential to mitigate the risk.
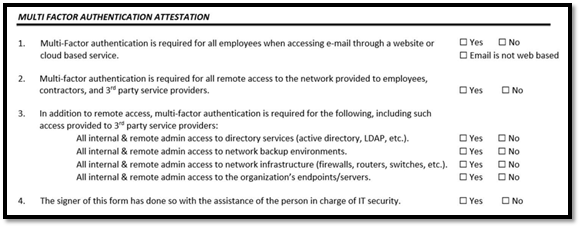 The controls described in the attestation are the minimum controls that must be in place to be eligible for a cyber risk policy. There have been recent instances of these controls being dramatically expanded, and this will likely continue as carriers struggle to deal with mounting claims.
The controls described in the attestation are the minimum controls that must be in place to be eligible for a cyber risk policy. There have been recent instances of these controls being dramatically expanded, and this will likely continue as carriers struggle to deal with mounting claims.
Gain Visibility of Your Entire Infrastructure with SIEM
A Security and Information Event Management (SIEM) solution collects and reviews logs—such as successful or failed logins or connections to internet sites—to detect anomalies and alert on them. SIEM as a Service (SIEMaaS) is an approach in which an organization collects the logs and securely sends them to an outsourced SIEM for analysis and alerting. An outsourced SIEM is managed by a third-party vendor’s security team and leverages the scale and collective expertise of the service provider while delivering the powerful benefits of holistic monitoring.
Secure Endpoints with Endpoint Detection and Response
Cybercriminals are relentless in finding ways to infiltrate your systems, especially targeting endpoints like servers and other devices with network access. Endpoint detection and response (EDR) solutions deliver centralized monitoring and logging of all endpoint activity across your enterprise, recognizing anomalous behavior to identify and remediate threats. EDR logs can also be fed into a SIEM for more comprehensive monitoring of your environment.
Conduct Regular Backups
Regardless of whether your institution is considering cyber insurance, it is a best practice to conduct frequent backups and determine your specific schedule based on your risk profile. Strengthen your protections further by ensuring encrypted backups are stored separately from your network or in a cloud environment and secure backups with different access credentials from other administrator credentials in conjunction with MFA.
Additionally, your institution should have a schedule for testing backups to ensure proper functionality, including testing the restoration and recovery of key server configurations and data backups in the last six months.
Understand that Cybersecurity is a Business Problem
While the security controls discussed above are important, they should be viewed as components of an institution’s larger cybersecurity strategy. Your institution should take a more strategic approach to cybersecurity and focus on objectives with meaningful impact on your overall risk profile, rather than simply chasing controls and checking boxes.
In our current environment, cyber liability insurance is a proven risk mitigation strategy. Take the time to invest upfront and develop a risk-based approach to assess the level of coverage you need.
For additional information on strengthening your cyber defenses, download our white paper.
GET MY COPY